this post was submitted on 04 Apr 2024
1020 points (98.8% liked)
linuxmemes
21273 readers
1542 users here now
Hint: :q!
Sister communities:
- LemmyMemes: Memes
- LemmyShitpost: Anything and everything goes.
- RISA: Star Trek memes and shitposts
Community rules (click to expand)
1. Follow the site-wide rules
- Instance-wide TOS: https://legal.lemmy.world/tos/
- Lemmy code of conduct: https://join-lemmy.org/docs/code_of_conduct.html
2. Be civil
- Understand the difference between a joke and an insult.
- Do not harrass or attack members of the community for any reason.
- Leave remarks of "peasantry" to the PCMR community. If you dislike an OS/service/application, attack the thing you dislike, not the individuals who use it. Some people may not have a choice.
- Bigotry will not be tolerated.
- These rules are somewhat loosened when the subject is a public figure. Still, do not attack their person or incite harrassment.
3. Post Linux-related content
- Including Unix and BSD.
- Non-Linux content is acceptable as long as it makes a reference to Linux. For example, the poorly made mockery of
sudoin Windows. - No porn. Even if you watch it on a Linux machine.
4. No recent reposts
- Everybody uses Arch btw, can't quit Vim, and wants to interject for a moment. You can stop now.
Please report posts and comments that break these rules!
Important: never execute code or follow advice that you don't understand or can't verify, especially here. The word of the day is credibility. This is a meme community -- even the most helpful comments might just be shitposts that can damage your system. Be aware, be smart, don't fork-bomb your computer.
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
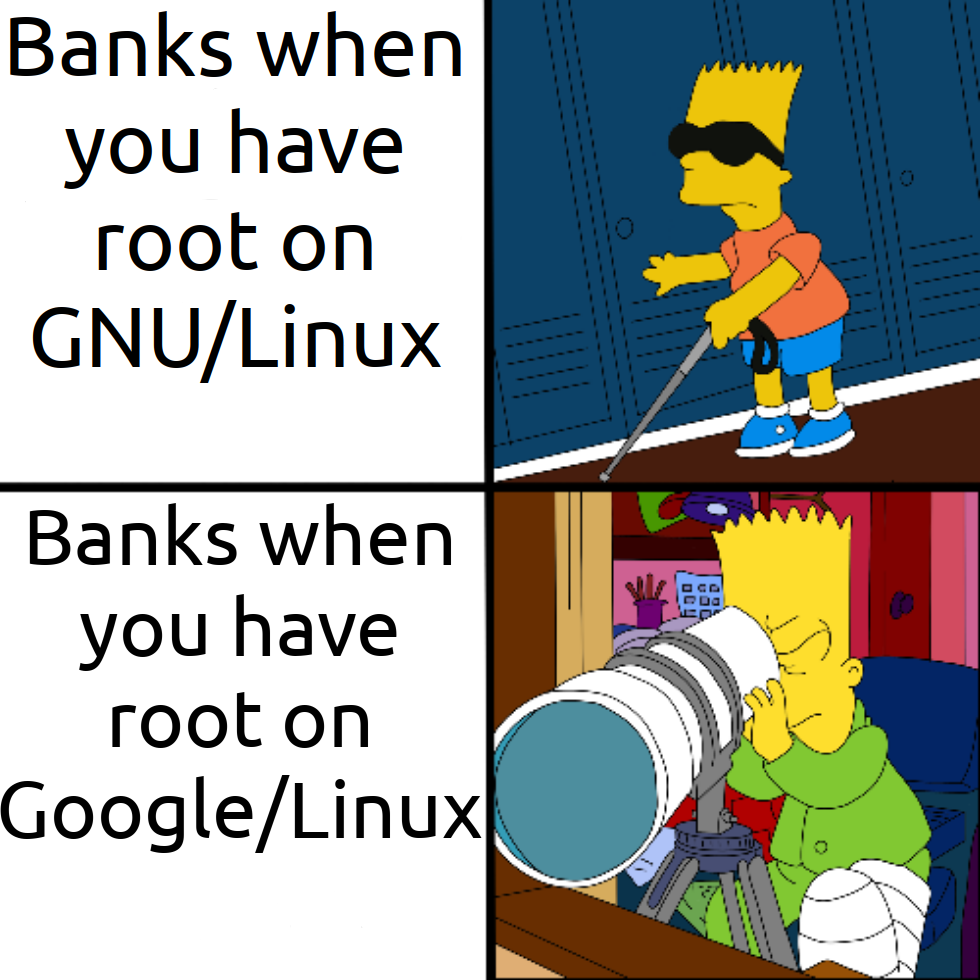
Rooted mobile devices are a reasonable signal they been have hacked and security features might be disabled or work as expected.
It just banks, a lot of corporate security polices don’t allow rooted devices, as they could bypass mobile device management policies for devices owned by the company.
With laptops it’s a different story. Whether users have Mac, Linux or Windows, there’s a reasonable chance they have admin access too, so checking for root access is not such a useful signal there.
Rooted mobile devices are a reasonable signal that someone wants to actually own what they buy, and corporations want to make sure as few people think that as possible.
Windows/Macos/Linux are designed around the fact that the person managing the device has root access, Android and iOS are designed around noone having root access.
Sure it's fine to mess around with rooted phone and look what's inside, but essentially for your daily operations having rooted phone is unnecessary security risk.
Yes and I consider that to mean I don't own the device. And there are plenty of Android forks specifically designed around you having root access.
The important question is why smartphones are designed around not having root access and computers are?
What are the incentives at play?
The answer is obvious, tech companies wouldn’t have given users access to root control on their computers either if they knew what they were doing and thought they could have gotten away with it.
It is just circular logic claiming smartphones have to be this way, circular logic that provides a rhetorical smokescreen for the process of corporations taking our agency away from us over our lives and the tools that sustain us.
You're free to install another operating system or variation on Android on your phone still. And if you decided to go with another Android such as Graphene, you'd still not want to root it because it's a security risk.
The issue is that you don’t want to give some random untrusted process root access. You, the user, have root access as long as you’re capable of running processes as root, but that doesn’t mean you should.
There could be tons of apps on the iOS App Store or Google Play Store that are completely benign under the existing security model but do nefarious things when run as root. No one knows that for sure because they aren’t tested under root by Apple or Google.
The problem with root is that it’s giving the process the keys to the Ferrari. That’s long since been decided to be a bad security model. Far better to have the process request permission to access particular resources and you grant them on a case by case basis.
It's been awhile since I've used anything but Magisk but usually you have to set root permissions per app, or you can get Magisk notification to request access.
I just want to point out, that what you are saying sounds good in an ideal world. But the realitiy looks different. (I actually typed out some points, but then I remembered that I don't want to engage in yet another lengthy internet-debate, that ultimately comes down to personal preferences and philosophy)
Ah but I love reading these specific philosophical discussions on tech, I don't blame you though