this post was submitted on 23 Apr 2024
279 points (98.6% liked)
Privacy
43125 readers
991 users here now
A place to discuss privacy and freedom in the digital world.
Privacy has become a very important issue in modern society, with companies and governments constantly abusing their power, more and more people are waking up to the importance of digital privacy.
In this community everyone is welcome to post links and discuss topics related to privacy.
Some Rules
- Posting a link to a website containing tracking isn't great, if contents of the website are behind a paywall maybe copy them into the post
- Don't promote proprietary software
- Try to keep things on topic
- If you have a question, please try searching for previous discussions, maybe it has already been answered
- Reposts are fine, but should have at least a couple of weeks in between so that the post can reach a new audience
- Be nice :)
Related communities
much thanks to @gary_host_laptop for the logo design :)
founded 6 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
How comes my useragent is Linux then? I just installed it fresh trom the arch official repos for the first time to test. Creepjs shows the useragent further down (not in this screenshot) and I visited other test sites as well.
I'll test it tomorrow by downloading it from the website.
Here some proof of my claim that Tor browser useragent string is Windows : https://wiki.archlinux.org/title/Firefox/Privacy#Change_user_agent_and_platform
From five years ago, afaik suggesting Windows is the default : https://gitlab.torproject.org/tpo/applications/tor-browser/-/issues/26146
~~Tor browser from the arch repos is not stock torbrowser. Add repos for torproject/guardian project/whatever it's called now, or use the torproject.org installer.~~
Yes it is. Since what the arch repos have is a script to download TB from torproject.org
You're thinking of F-Droid (on Android), at least that is what the Guardian Project repo is for.
Thanks for the correction.
Are you saying that Arch Linux is providing Tor browser with a different useragent string ?
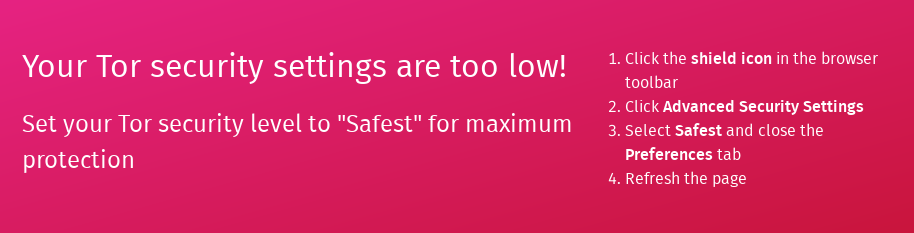
I believe that is the case, if you inspected the HTTP headers and found if to show Linux instead of Windows. my last experience with that would have been years ago. Arch does like to compile things from source instead of using binary blobs, and compilers and configs can undo a lot of the work the torproject has done to combat fingerprinting, which is why it's recommended to run the pre-built binary and install no plugins. However it's important to note that it ALSO gives you a unique JavaScript fingerprint every time, when tools use as much information as possible to generate a fingerprint, because it generates new information on every reload. That's why OPSEC is important and for can't help you if you use it wrong. If you login to 2 different unlinked sites in the same session, and you don't want them to be linked, too bad now they're linked via JS fingerprinting. JavaScript is more or less a programming language within the browser, and you'll never escape JavaScript fingerprinting. Which is why it's important to learn how to use tor properly, and leave JS disabled as much as you can.
One thing you can do with your arch build is use the fingerprinting tool to see how unique you are, then get a new identity, then go back and do it again. Does it now say you're one of 2 people who have used the tool, or does it show you're (again) unique? If the latter, then it's working (at least enough) properly.
Interesting. I would have expected the useragent string to be part of the user configuration files that are automatically created in the browser profile directory. I've not used Tor browser package from Arch yet but curious to do some testing.
torbrowser-launcher (found in the extra repo) simply downloads Tor Browser from torproject.org, unless you use some AUR version of Tor Browser that recompiles it, you are getting the exact same TB as you would by manually downloading it.
Thanks. AUR seems to only have a Tor browser bin which does not recompile.
Edit. I see what you mean now. CreepJS indeed shows userAgent Linux. Weird. It got the amount of cores wrong btw.
Becuase creepjs uses JS to figure out the userAgent, WorkerNavigator.userAgent