this post was submitted on 18 Nov 2024
977 points (99.6% liked)
Technology
77096 readers
3783 users here now
This is a most excellent place for technology news and articles.
Our Rules
- Follow the lemmy.world rules.
- Only tech related news or articles.
- Be excellent to each other!
- Mod approved content bots can post up to 10 articles per day.
- Threads asking for personal tech support may be deleted.
- Politics threads may be removed.
- No memes allowed as posts, OK to post as comments.
- Only approved bots from the list below, this includes using AI responses and summaries. To ask if your bot can be added please contact a mod.
- Check for duplicates before posting, duplicates may be removed
- Accounts 7 days and younger will have their posts automatically removed.
Approved Bots
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
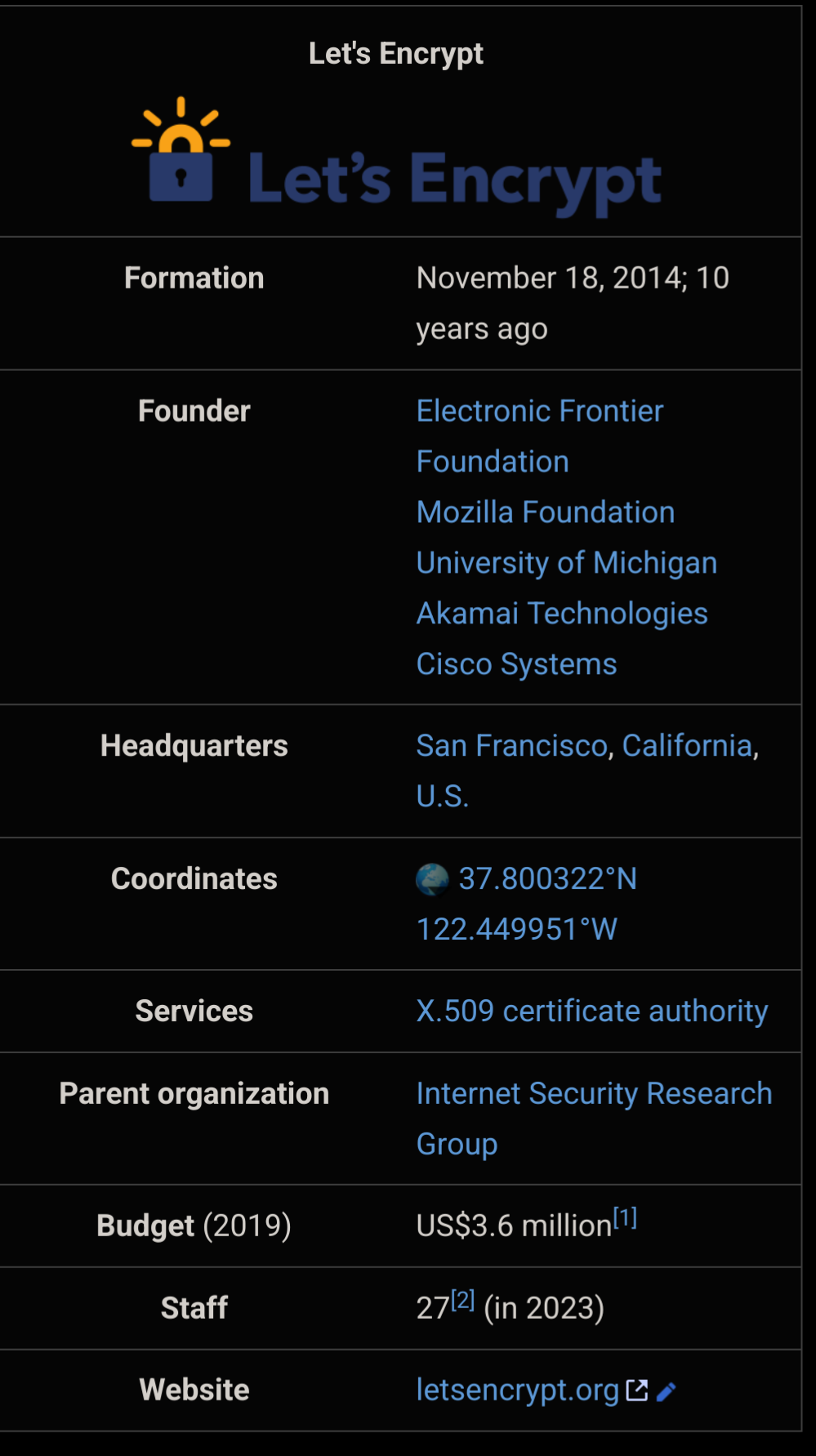
Let's Encrypt is amazing, but are there any equally trustworthy alternatives people could switch to if something bad happens to it?
They came up with the ACME protocol, so presumably somebody could. The real barrier to entry is the cost of getting into that certificate chain of trust. I have no idea why it's so difficult and expensive.
Well, it's difficult, as it should be, because if you control a certificate in the active chain of trust of browsers, you can hack pretty much anything you want.
Correct me if I'm wrong, but isn't the CA only signing your public key to prove identity/authority? I don't think the CA can magically MITM every cert they sign.
The impact is not serious enough to warrant a $1m entry fee, IMO. At best, someone could impersonate a site. They'd also have to get other things in line (e.g. DNS hijacking) to be at all successful anyway. And it's not like most people are authenticating certs themselves. They just trust browsers to trust CAs that vouch for you and prevents those scary browser warnings.
It doesn't improve encryption compared to a self-signed cert though.
If you are the CA, you can sign a new certificate yourself for google.com and the browser will accept it. It's effectively allows MITM for any certificate. Worse, it's not even limited to certificates under that CA. The browser has no way of knowing there's 2 "valid" certs at once, and in fact that is allowed regardless (multiple servers with different instances of the SSL cert is a possibility).
Certificate pinning might save things, since that will force the same certificate as was previously used, but I'm not sure this is a common default.
If it begins to enshitify, someone will quickly take up the helm. It's become so core now that someone like Cloudflare would just be like "We do this now."
Cloudflare sort of provides this now by being a MITM to secure your site between your server and the end user. But this requires you and your end user to trust Cloudflare.
And fwiw the ACME protocol is open so anyone can implement it. I believe even the ACME software that EFF sends out allows you to choose your server with some configuration.
Yup, it does. I think I still have my server hard coded from when it first launched.
Cloudfare means no click from me (TBH after I clicked)
I think Cloudflare enshittifying is a bigger risk that Let's Encrypt.
Maybe ZeroSSL
They don't offer wildcard certs, but otherwise I think they are.
I wanna say acme.sh defaults to them.
Never used them, but they state at https://zerossl.com/features/acme/ that their free acme certs include wildcards.
Yes, seems you are right. Not sure where I got the impression.
Unrelated, when I researched this I saw that acme.sh, zerossl, and a bunch of other acme clients are owned by the same entity, "Stack Holdings"/"apilayer.com". According to this, zerossl also has some limitations over letsencrypt in account requirements and limits on free certificates.
It is suspicious that they impose so many restrictions then waive most on the acme api, where they presumably could not compete otherwise. On their gui they allow only 3 certificates and don't allow multi-domain at all. Then even in the acme client they somehow push an account into the process.
This all does make me slightly worry this block around apilayer.com will fall before letsencrypt does.
Other than letsencrypt and zerossl, this page also lists no other full equivalents for what letsencrypt does.
I think if LetsEncrypt went away, so would ZeroSSL's free offer.
However, I do think not having limitations on the API is good; automation is good practice and I guess this is a concession to customers /users who have no automation in place (though this is a sad state by now). LE doesn't offer anything comparable AFAIK.
ZeroSSL, plus a few paid companies support ACME (I know Sectigo and GoDaddy do). Sure, the latter are paid services, but in theory you can switch to them and use the exact same setup you're currently using with Let's Encrypt, just with some config changes.