cross-posted from: https://lemmy.ml/post/20536177
+-----------------+ | . local server | +-.---------------+ < . > < . > < . > < . > < . > +-.-----------------------+ | . serveo/localhost.run | +-.-----------------------+ < . > < . > +----------------------+ < . > | . raw data | < . > | < . > encrypted data | < . > +----------------------+ +-.----------+ | . clients | +------------+hellow,
i wanna host things (nextcloud, bin, syncthing) myself but im under cg nat so i cant do it the regular way. i have to tunnel my way out. the only concern is that, the raw data is readable by the ssh server (ie. serveo/localhost.run), but i dont anyone elses eyes on my data
sorry for my broken english.
edit:
- syncthing (solved): https://docs.syncthing.net/users/untrusted.html
- bin (solved): https://github.com/HemmeligOrg/Hemmelig.app?tab=readme-ov-file#features
- nextcloud: ???
please clarify me.
if i setup a vpn which provides encryption on my local server, can i go like this
+------------------+ | . local server | +-< . >------------+ << . >> << . >> << . >> << . >> << . >> +-< . >----------------------+ | < . > serveo/localhost.run | +-< . >----------------------+ << . >> << . >> +-------------------------------------+ << . >> | . raw data | << . >> | < . > vpn encrypted data | << . >> | << . >> vpn encrypted data over tls | << . >> +-------------------------------------+ +-< . >-------+ | . clients | +-------------+sorry i dont know how to express this in words
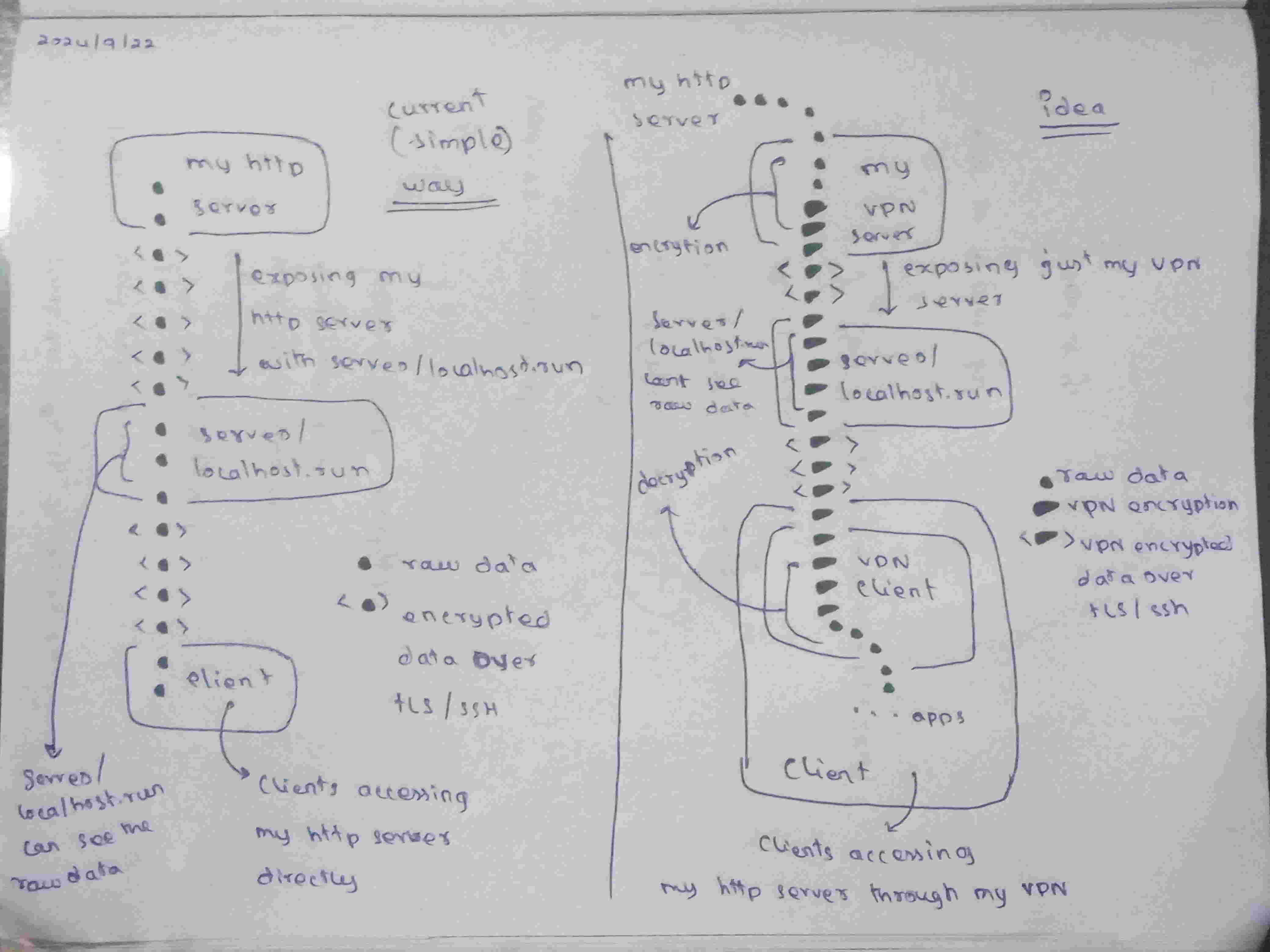
this is what i was trying to say. so the idea, is that okay?